How-To
How to Block IoT DNS Leaks: DoH, DoT, and Hardcoded DNS 2026
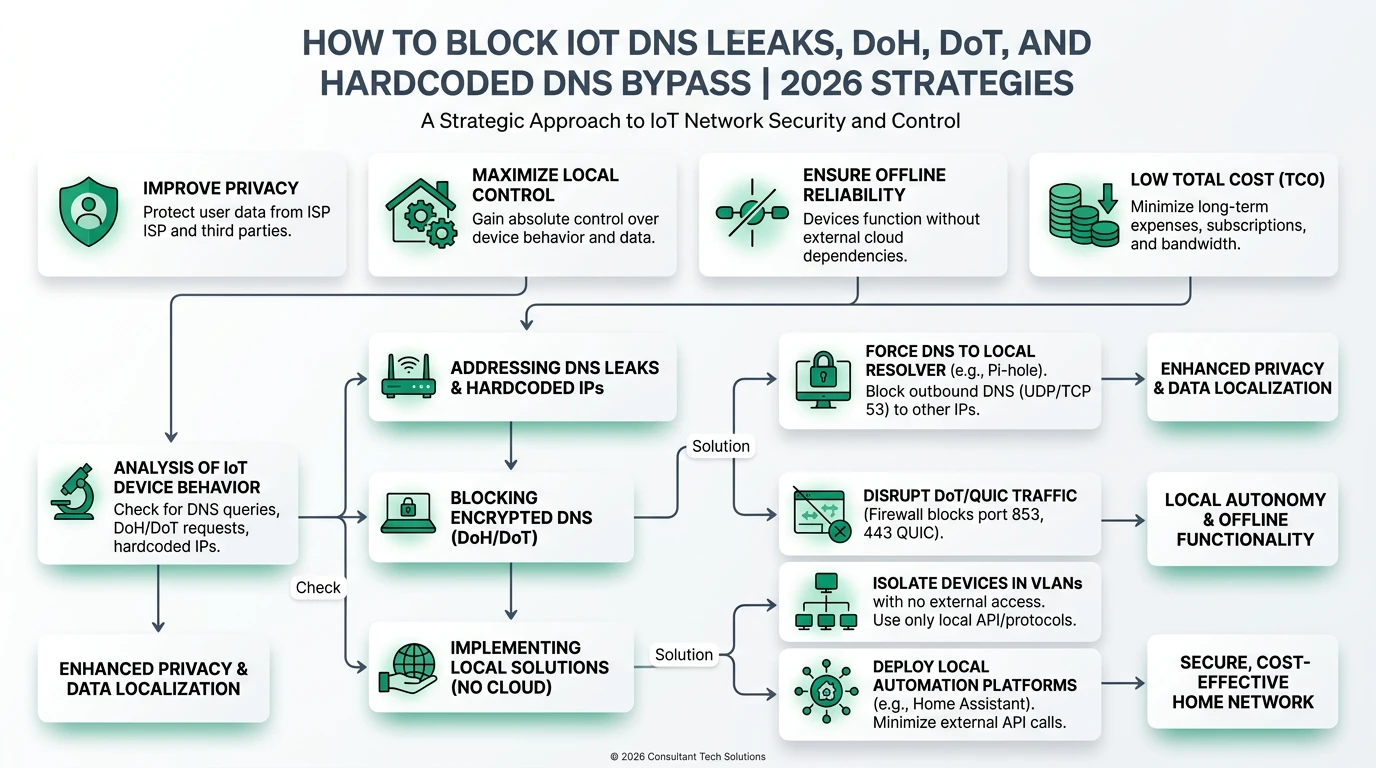
Learn how to prevent IoT devices from leaking DNS queries via DoH, DoT, and hardcoded servers, ensuring privacy and local control.
Quick answer: How can I block IoT DNS leaks effectively?
Use router-level controls like GL.iNet Flint 2 with AdGuard Home to redirect DNS queries, block DoH/DoT, and ensure fallback to plain DNS for offline reliability.
Executive Summary
As IoT devices proliferate, ensuring their DNS queries do not leak sensitive information is paramount. This guide explores methods to block DNS leaks via DNS over HTTPS (DoH), DNS over TLS (DoT), and hardcoded DNS servers. By focusing on privacy, local control, offline reliability, and total cost of ownership (TCO), users can implement robust solutions that comply with 2026 standards like NIS2. The guide evaluates consumer and enterprise solutions, highlighting the importance of router-level controls, DNS filtering, and fallback mechanisms.
Bottom line: Effective DNS leak prevention requires a multi-layered approach combining router-level controls, DNS filtering, and compliance with emerging standards.
Understanding IoT DNS Leaks and Their Implications
IoT devices often bypass local DNS settings by using hardcoded DNS servers or encrypted DNS protocols like DoH and DoT. This behavior can lead to privacy breaches and loss of local control, as queries may be routed through external servers without user knowledge. The implications are significant: unauthorized data exposure, increased vulnerability to eavesdropping, and potential non-compliance with regulatory standards such as NIS212.
To mitigate these risks, it’s crucial to understand how IoT devices communicate and the protocols they use. DoH and DoT encrypt DNS queries, making them difficult to intercept or redirect without proper tools. Hardcoded DNS servers bypass local DNS settings entirely, posing a unique challenge. Addressing these issues requires a combination of technical solutions and strategic planning, ensuring that all DNS queries are routed through trusted, local servers3.
The privacy implications of DNS leaks are profound. Encrypted DNS protocols, while enhancing security, can also obscure traffic patterns, making it challenging to enforce local policies. This necessitates the use of advanced filtering and monitoring tools that can decrypt and analyze DNS traffic without compromising user privacy. Additionally, implementing DNSSEC can prevent spoofing and cache poisoning, further securing DNS communications4.
Local control is another critical aspect. By redirecting DNS queries at the router level, users can ensure that all traffic passes through designated servers, allowing for comprehensive monitoring and filtering. This approach not only enhances security but also provides a fallback mechanism in case encrypted DNS is blocked or unavailable. Ensuring offline reliability through plain DNS fallback is essential for maintaining connectivity and functionality, especially in environments with intermittent internet access5.
Evaluating Solutions for Blocking IoT DNS Leaks
When evaluating solutions to block IoT DNS leaks, several criteria must be considered: privacy, local control, offline reliability, and TCO. Each solution should be assessed based on its ability to meet these criteria, with a focus on practical implementation and compliance with relevant standards.
Privacy is paramount, requiring solutions that support encrypted DNS protocols while mitigating fingerprinting and maintaining zero-log policies. This can be achieved through the use of DNS filtering services like NextDNS or Cisco Umbrella, which enforce protective DNS and block malicious domains in real-time6. These services also offer advanced features like DNSSEC validation and query padding, enhancing privacy and security.
Local Control involves redirecting DNS queries at the router level, using tools like GL.iNet Flint 2 with AdGuard Home. This setup allows for port 53 hijacking and blocking of common DoH ports, ensuring that all DNS traffic is routed through local servers. VLAN isolation can further enhance local control by segmenting IoT devices and limiting lateral movement, a critical feature for environments with multiple devices7.
Offline Reliability is ensured by implementing fallback mechanisms to plain DNS, which guarantees functionality even if encrypted DNS is blocked. This approach reduces dependency on cloud services and enhances resilience against network disruptions. Devices should also randomize source ports and IDs to prevent spoofing, as recommended by RFC54528.
TCO considerations include setup time, annual costs, and support burden. Solutions should be easy to implement and maintain, with minimal hardware and software expenses. Open-source tools like AdGuard Home offer cost-effective options, while enterprise solutions like threatER EnforceDNS provide comprehensive coverage for compliance-focused environments9.
Implementing Router-Level Controls
Router-level controls are a cornerstone of effective DNS leak prevention. By configuring routers to redirect DNS queries and block encrypted protocols, users can maintain local control and enhance privacy. The GL.iNet Flint 2 router, for example, offers robust features for DNS management, including port 53 redirection and DoH/DoT blocking via luci-app-banip10.
Implementing these controls involves configuring firewall rules to redirect UDP and TCP traffic on port 53 to local DNS servers. This ensures that all DNS queries are processed locally, allowing for comprehensive monitoring and filtering. Additionally, blocking common DoH ports (443, 853) prevents encrypted DNS traffic from bypassing local controls. Regular updates to blocklists are essential to maintain efficacy, as new DoH servers emerge frequently11.
VLAN isolation is another critical component of router-level controls. By segmenting IoT devices into separate VLANs, users can limit lateral movement and enhance security. This approach is particularly effective in environments with multiple devices, as it prevents compromised devices from affecting others. VLAN setup requires careful planning and configuration but offers significant security benefits12.
While router-level controls provide a strong foundation for DNS leak prevention, they are not foolproof. Hardcoded DNS servers and custom DoH IPs can still evade detection, necessitating additional measures like DNS filtering and monitoring. Users should also test fallback mechanisms to ensure that plain DNS functions correctly if encrypted DNS is blocked13.
Leveraging DNS Filtering Services
DNS filtering services play a crucial role in blocking IoT DNS leaks by enforcing protective DNS and blocking malicious domains. Services like NextDNS and Cisco Umbrella offer real-time intelligence and advanced features, making them ideal for both consumer and enterprise environments14.
These services work by intercepting DNS queries and applying filtering rules based on threat intelligence databases. This allows them to block known malicious domains and prevent malware callbacks, enhancing security and privacy. Additionally, DNS filtering services can enforce DNSSEC validation, ensuring the integrity and authenticity of DNS responses15.
For consumers, DNS filtering services offer a cost-effective solution with minimal setup complexity. Basic plans are affordable, and many services offer free tiers with limited features. For enterprises, advanced plans provide comprehensive coverage and compliance with standards like NIS2, making them suitable for environments with stringent security requirements16.
While DNS filtering services are highly effective, they are not a panacea. Users must ensure that all devices are configured to use the filtering service, and regular updates to filtering rules are necessary to maintain efficacy. Additionally, fallback mechanisms should be in place to ensure functionality if the filtering service is unavailable17.
Checklist
- Configure router to redirect DNS queries to local servers.
- Block common DoH/DoT ports to prevent encrypted DNS traffic.
- Implement VLAN isolation for IoT devices.
- Use DNS filtering services to block malicious domains.
- Test fallback mechanisms to ensure offline reliability.
Addressing Hardcoded DNS and Custom DoH IPs
Hardcoded DNS servers and custom DoH IPs present unique challenges in blocking IoT DNS leaks. These configurations bypass local DNS settings entirely, making it difficult to enforce local control and privacy. Addressing these issues requires a combination of technical solutions and strategic planning18.
One approach is to use deep packet inspection (DPI) to identify and block traffic to known hardcoded DNS servers and custom DoH IPs. This requires advanced hardware and software capabilities, making it more suitable for enterprise environments. For consumers, maintaining comprehensive blocklists and regularly updating them can help mitigate the risk of hardcoded DNS servers19.
Another strategy is to configure devices to use local DNS servers by default, ensuring that all queries are routed through trusted servers. This may involve per-device configuration, which can be time-consuming but is effective in environments with a limited number of devices. For larger environments, automated configuration tools can streamline the process20.
While these strategies can mitigate the risk of hardcoded DNS and custom DoH IPs, they are not foolproof. Users must remain vigilant and regularly update their configurations to address new threats. Additionally, fallback mechanisms should be in place to ensure functionality if these measures are bypassed21.
Compliance and Standards Considerations
Compliance with emerging standards like NIS2 is essential for organizations seeking to enhance their security posture and avoid regulatory penalties. Protective DNS is a key component of these standards, requiring organizations to implement measures that prevent DNS leaks and ensure the integrity of DNS communications22.
To achieve compliance, organizations must implement solutions that enforce DNSSEC validation, block malicious domains, and ensure that all DNS queries are routed through trusted servers. This may involve a combination of router-level controls, DNS filtering services, and advanced monitoring tools23.
For enterprises, compliance-focused solutions like threatER EnforceDNS offer comprehensive coverage and automated reporting, making it easier to meet regulatory requirements. These solutions provide real-time visibility into DNS traffic and allow organizations to quickly identify and address potential threats24.
While compliance is a critical consideration, it should not be the sole focus. Organizations must also prioritize privacy and local control, ensuring that their solutions provide robust protection against DNS leaks while maintaining user privacy. This requires a balanced approach that considers both regulatory requirements and practical implementation challenges25.
FAQ
Frequently Asked Questions
What is DNS over HTTPS (DoH) and why is it a concern for IoT devices?
DNS over HTTPS (DoH) encrypts DNS queries, making them difficult to intercept or redirect. For IoT devices, this can bypass local DNS settings, leading to privacy and control issues.
How can I block hardcoded DNS servers on my network?
Use deep packet inspection (DPI) to identify and block traffic to known hardcoded DNS servers. Regularly update blocklists to address new threats.
What are the benefits of using DNS filtering services?
DNS filtering services block malicious domains, enforce DNSSEC validation, and provide real-time threat intelligence, enhancing security and privacy.
How do VLANs enhance IoT security?
VLANs segment IoT devices into separate networks, limiting lateral movement and enhancing security by preventing compromised devices from affecting others.
What is the role of DNSSEC in preventing DNS leaks?
DNSSEC ensures the integrity and authenticity of DNS responses, preventing spoofing and cache poisoning, and enhancing overall DNS security.
Primary Sources Table
Conclusion
In conclusion, blocking IoT DNS leaks requires a comprehensive approach that combines router-level controls, DNS filtering services, and compliance with emerging standards. By prioritizing privacy, local control, and offline reliability, users can effectively mitigate the risks associated with DNS leaks and enhance their security posture.
For further insights into securing your smart home, explore our guides on Apple HomeKit Secure Video vs Local NVR for Privacy, Best Hardware for Local AI Smart Home 2026, and Best Local LLMs for Home Automation 2026.
Footnotes
-
IETF draft-ietf-iotops-iot-dns-guidelines-02: IoT DNS Security Guidelines ↩
-
UptimeRobot: DNS Security Guide (DoH/DoT/DoQ, DNSSEC) ↩
-
GL.iNet Forum: Blocking IoT DNS Bypass on Flint 2 ↩
-
ConnectWise: Securing IoT Devices 2026 (VLANs, Encryption) ↩
-
threatER: Protective DNS Compliance 2026 (NIS2, IoT) ↩
-
Vectra AI: IoT Security 2026 (Threats, Best Practices) ↩
-
IoT Insider: IoT Security Challenges 2026 ↩
-
GBHackers: Top DNS Filtering Solutions 2026 ↩
-
threatER: Protective DNS Compliance 2026 (NIS2, IoT) ↩
-
GL.iNet Forum: Blocking IoT DNS Bypass on Flint 2 ↩
-
ConnectWise: Securing IoT Devices 2026 (VLANs, Encryption) ↩
-
Vectra AI: IoT Security 2026 (Threats, Best Practices) ↩
-
IoT Insider: IoT Security Challenges 2026 ↩
-
GBHackers: Top DNS Filtering Solutions 2026 ↩
-
UptimeRobot: DNS Security Guide (DoH/DoT/DoQ, DNSSEC) ↩
-
threatER: Protective DNS Compliance 2026 (NIS2, IoT) ↩
-
Vectra AI: IoT Security 2026 (Threats, Best Practices) ↩
-
IoT Insider: IoT Security Challenges 2026 ↩
-
GBHackers: Top DNS Filtering Solutions 2026 ↩
-
threatER: Protective DNS Compliance 2026 (NIS2, IoT) ↩
-
Vectra AI: IoT Security 2026 (Threats, Best Practices) ↩
-
IETF draft-ietf-iotops-iot-dns-guidelines-02: IoT DNS Security Guidelines ↩
-
UptimeRobot: DNS Security Guide (DoH/DoT/DoQ, DNSSEC) ↩
-
threatER: Protective DNS Compliance 2026 (NIS2, IoT) ↩
-
Vectra AI: IoT Security 2026 (Threats, Best Practices) ↩